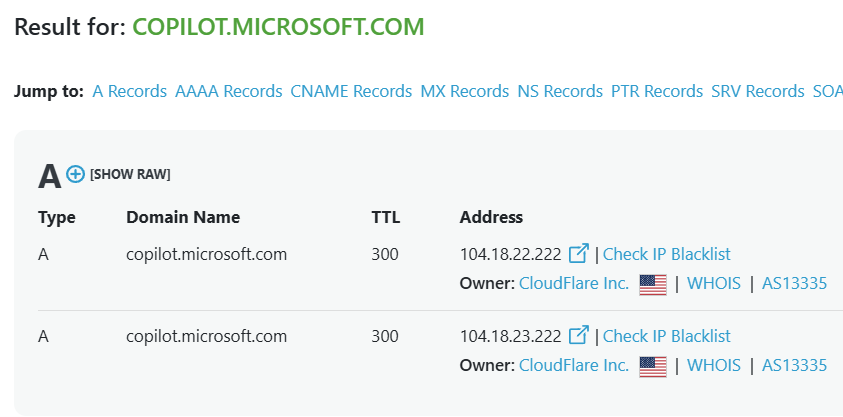
We did some sleuthing into our own data to find the most popular websites in the world that are using Cloudflare in some capacity: whether it's simply as a CDN, as a WAF, or to power their backend applications using Workers. There were actually a few surprising sites you would never expect to be using CloudFlare...
Artificial Intelligence · San Francisco, CA · ChatGPT, DALL·E, OpenAI API
Cloudflare
OpenAI is the company behind ChatGPT, the chatbot that more or less kicked off the current AI boom. They also make image generators, voice models, and APIs that other developers build their own AI products on. Hundreds of millions of people use their tools every week.
Cloudflare sits in front of every door into OpenAI's systems. The consumer chatbot, the developer API, and the internal endpoints that power conversations all route through Cloudflare first.
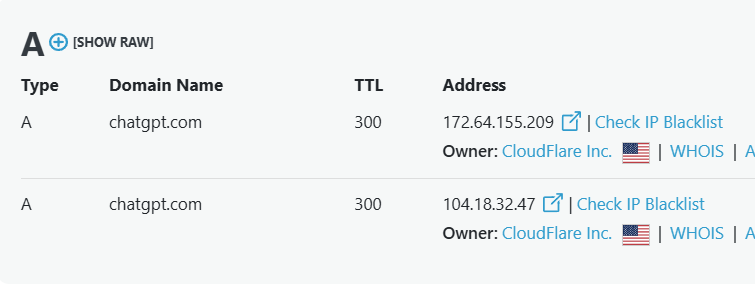
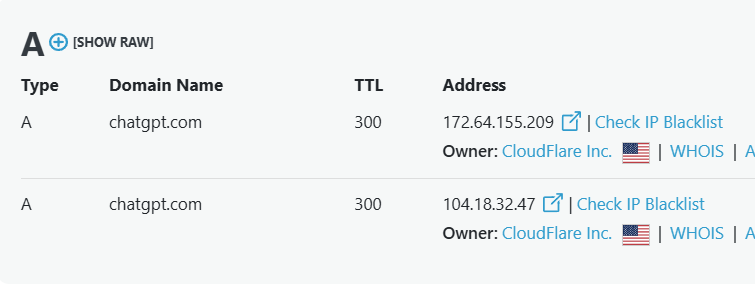
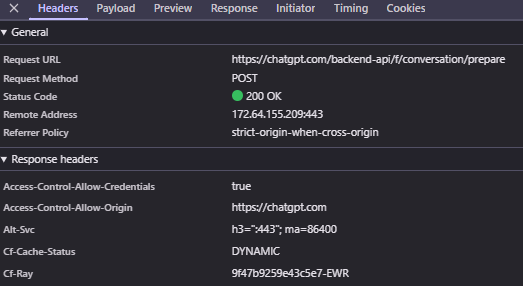
Start with chatgpt.com. The DNS records point straight at Cloudflare's network. When you type a question into ChatGPT, the first thing your request hits isn't OpenAI's servers, it's Cloudflare's.
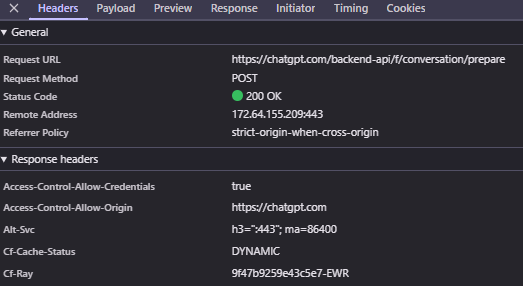
The backend that runs the conversations is the same. When the chat interface prepares a new conversation, the response headers give it away with a CF-Ray field. CF-Ray is the unique ID Cloudflare stamps on every request it handles, which is the easiest way to confirm a site is running through their network.
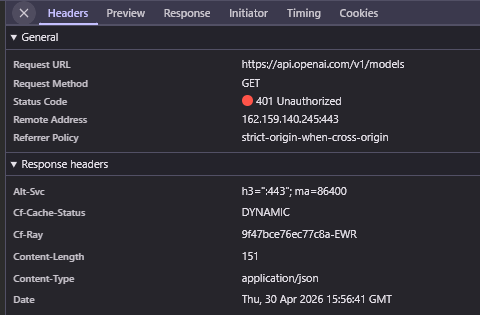
The developer API runs the same way. A request to api.openai.com, the endpoint companies pay billions of dollars a year to call, is answered by Cloudflare first.
Beyond protecting traffic, OpenAI uses Cloudflare as part of how their infrastructure routes requests around the world. Their cloud team has described a stack where Kubernetes clusters in multiple regions sit behind a service mesh and a global load balancing layer built on Cloudflare. So Cloudflare isn't just blocking bad traffic, it's helping decide which data center should handle each request based on where the user is.
The marketing site at openai.com is built on the same foundation, alongside Microsoft Azure, Kubernetes, and Terraform. Casual visitor reading a blog post, paying ChatGPT user, or developer hitting the API: same provider on the front door for all of them.
Software · Redmond, WA · Windows, Office, Azure, Copilot, LinkedIn
Cloudflare
Cloudflare Bot Management
Cloudflare Turnstile
Cloudflare Access
Microsoft is the company behind Windows, Office, and Azure. They sell software, cloud computing, video games, and AI tools to billions of people and millions of businesses. They also operate one of the largest cloud platforms in the world, which competes directly with Cloudflare in some areas.
Which makes it striking where Cloudflare shows up inside Microsoft. Their flagship AI product, Copilot, runs on a competitor's infrastructure.
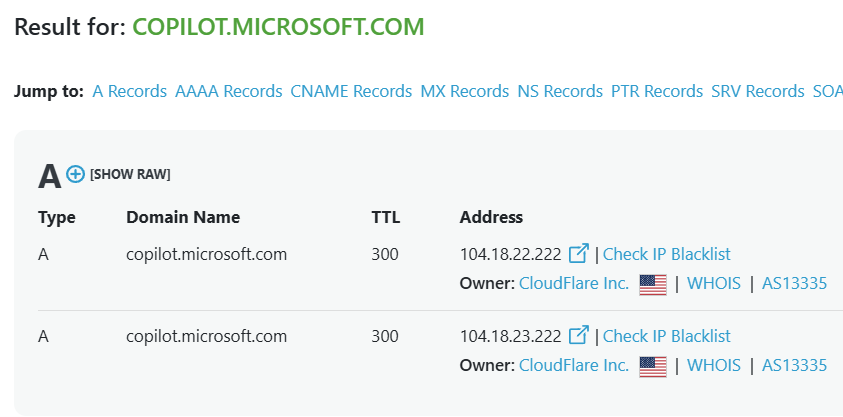
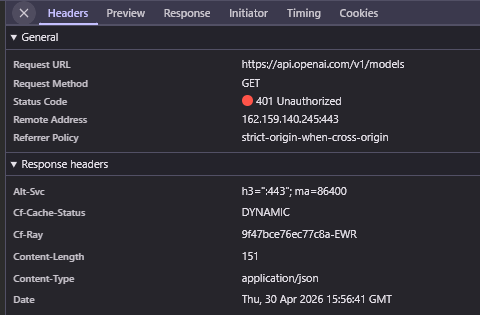
Copilot is Microsoft's answer to ChatGPT, the chatbot they're betting their AI strategy on, integrated into Windows, Office, and Edge. Its DNS records point straight to Cloudflare. So when a Microsoft customer asks Copilot a question, Cloudflare answers before Microsoft's own infrastructure ever sees the request.
That's a striking choice given Microsoft owns Azure, which has its own competing edge product called Azure Front Door. But for their most prominent AI product, they've put a competitor in the path. And not just for basic CDN. Copilot also runs Cloudflare Bot Management on every visitor and uses Cloudflare Turnstile in the abuse report flow when users flag harmful AI content.
Why pick a competitor for all of this? The most likely answer is scale and specialization. Generative AI products are a magnet for abuse: prompt injection bots, scraping at high volume, account takeover attempts, and people trying to extract training data. Cloudflare's bot management has been battle-tested across millions of customer sites for years. Azure's equivalents are newer and less proven on this exact problem. For a brand-new product where reliability matters more than ideology, Microsoft picked the tool with the longer track record.
Cloudflare also shows up across Microsoft's many acquisitions. Many of these companies were running on Cloudflare before being bought, and rather than force a migration to Azure, Microsoft has left the existing setups in place.
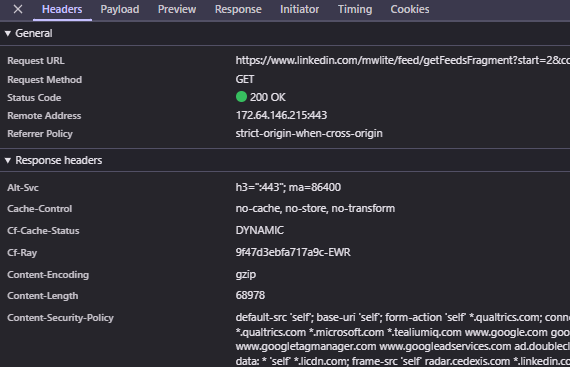
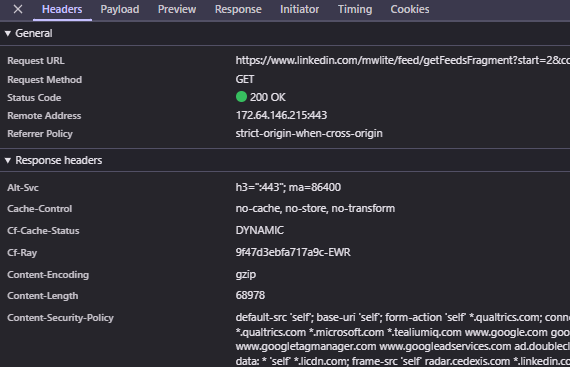
LinkedIn is the clearest example. Microsoft bought it in 2016, and most of its infrastructure has moved to Microsoft's own systems, but pieces still touch Cloudflare. Scroll your LinkedIn feed and some of the background API calls that load posts come back with a CF-Ray header, a small piece of the original stack that survived the migration.
Social Media · San Francisco, CA · X platform, X API
Cloudflare
Cloudflare Zero Trust
X is the social media platform formerly known as Twitter. People use it to post short messages, follow public conversations, and get news in real time. Hundreds of millions of users sign in every day, and developers and businesses use it through an API to build their own apps and tools.
At X, Cloudflare runs from the front of the house all the way to the back office. The public website, the developer API, and even the logins their own employees use to do their jobs all flow through it.
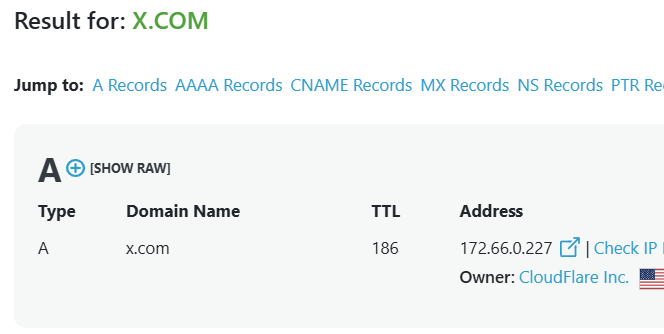
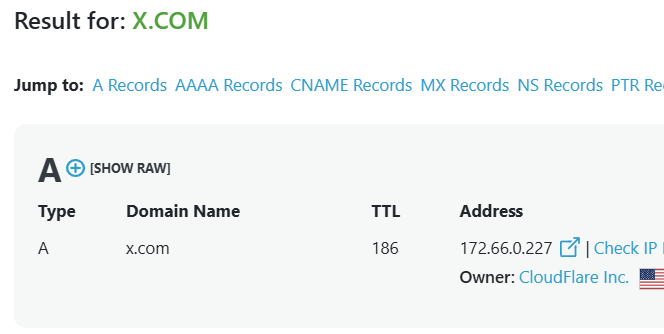
The website is the obvious entry point. The DNS record for x.com points to Cloudflare, so every visit lands on Cloudflare before it ever reaches X's own servers.
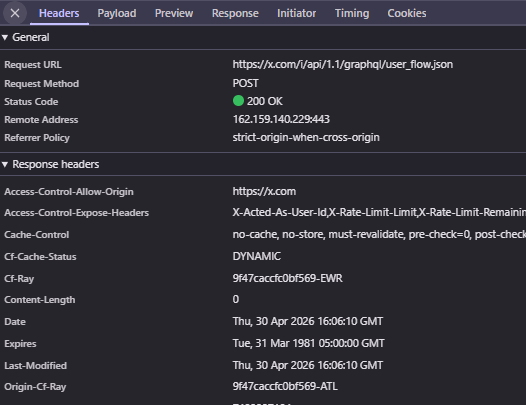
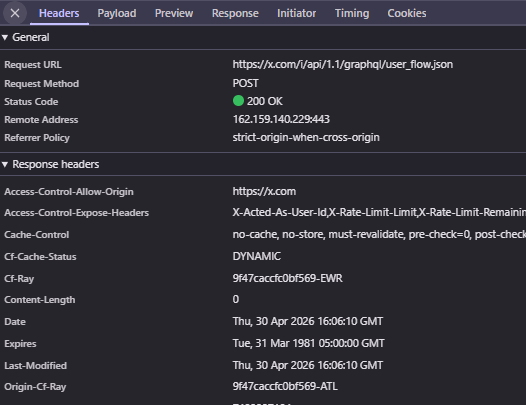
The same goes for the front-end API the website uses behind the scenes. When you scroll through your feed or load a profile, X is constantly making background requests to its own internal endpoints, and those come back with a CF-Ray header too.
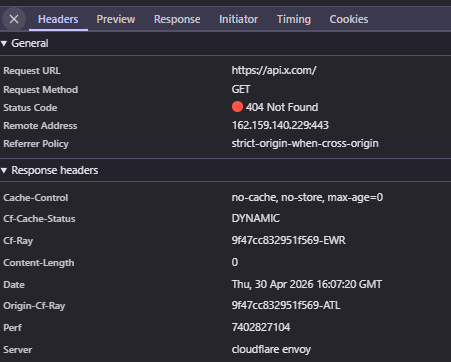
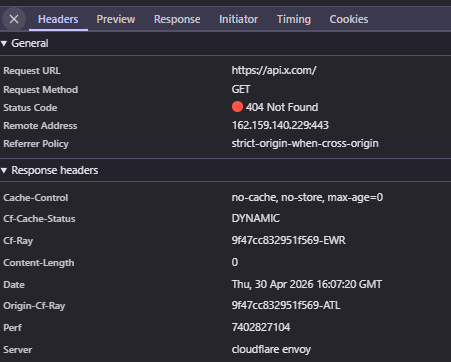
The developer API at api.x.com runs the same way, with one extra wrinkle. The response headers identify the server as "cloudflare_envoy," a setup that combines Cloudflare with Envoy, an open-source proxy that helps route traffic between services. So the same provider that protects the consumer website also fronts the API that thousands of businesses build their products on top of.
What's less expected is how X handles employee access. The company has built its security model around Cloudflare Zero Trust, the suite of products that replaces traditional VPN access. Instead of putting people on a VPN to reach internal apps, employees authenticate through Cloudflare every time they need access. The company has been building this out for years, and Cloudflare is one of the central platforms they pull signals from when deciding who gets to see what.
Pharmaceutical Manufacturing · North Chicago, IL · 60,000+ employees
CDN
WAF
Workers
Magic Transit
Magic Firewall
Access
Argo
Load Balancing
DNS
Bot Management
AbbVie is one of the world's biggest drug companies, behind medicines for things like immune disorders, cancer, and eye care. They're a 60,000-person operation selling to hospitals, pharmacies, and patients around the world.
The interesting thing is that AbbVie runs almost everything through Cloudflare. It's not just a security tool sitting in front of one website. It's the global edge network for their applications, handling how traffic gets routed, cached, and protected across the internet.
That means a lot of different jobs all running on the same platform. Cloudflare's CDN speeds up how their apps load. The web application firewall and bot management tools block bad traffic before it hits anything important. DNS handles the routing, with failover rules so things keep working if a server goes down. And Workers, which is Cloudflare's code-at-the-edge product, lets their team run logic right on the network itself instead of inside their data centers.
They also use Cloudflare for the deeper plumbing. Magic Transit and Magic Firewall protect their broader network from attacks, not just their websites. Cloudflare Access controls who can log in to internal tools. Argo and Load Balancing keep traffic moving along the fastest path.
To keep all of this manageable, the team treats their Cloudflare setup like code. They use Terraform and CI/CD pipelines to push changes, so a new firewall rule or DNS update goes through the same review process as any other software change. That keeps a global pharmaceutical company's edge network from drifting into chaos.
 Shopify
Shopify
E-commerce · Ottawa, Canada · Online store software
Cloudflare
Shopify is the software powering millions of online stores, from one-person candle shops to brands doing nine figures in sales. If you've checked out as a guest on a small brand's site, you've probably used it.
What's notable about Shopify's Cloudflare usage isn't that they use it. It's that they've put every customer touchpoint on it, from the storefronts shoppers buy from to the back-office tools merchants use to run their business.
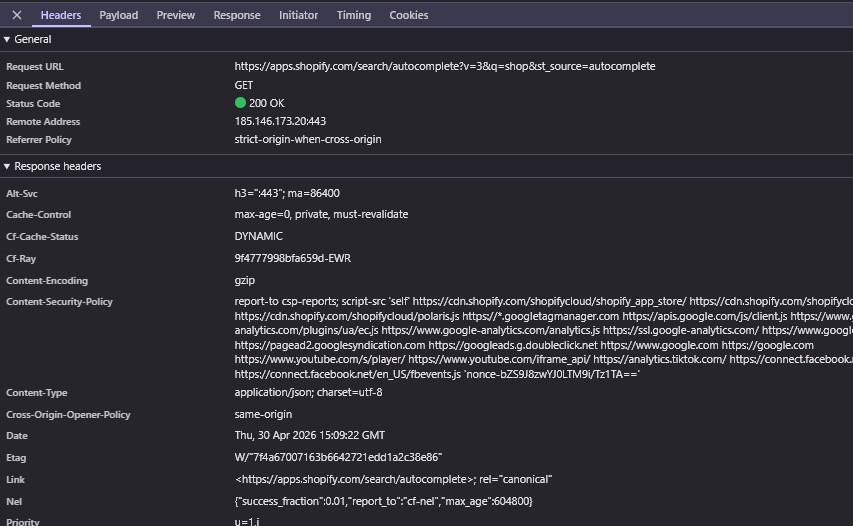
Every Shopify storefront, regardless of size, routes through Cloudflare. When a shopper loads a product page on any of millions of Shopify-hosted stores, Cloudflare answers before Shopify's own servers see the request.
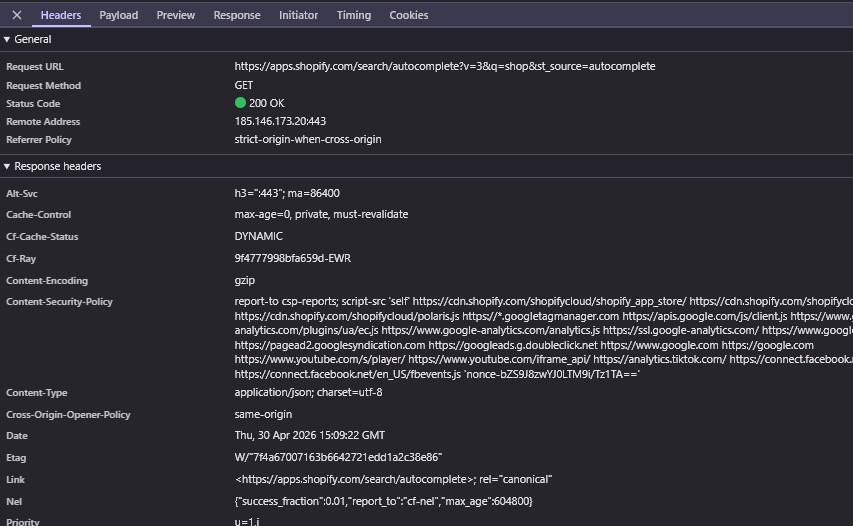
The merchant side runs the same way. The search inside the Shopify App Store, where store owners hunt for apps to add reviews, loyalty programs, or shipping tools, sits behind Cloudflare too.
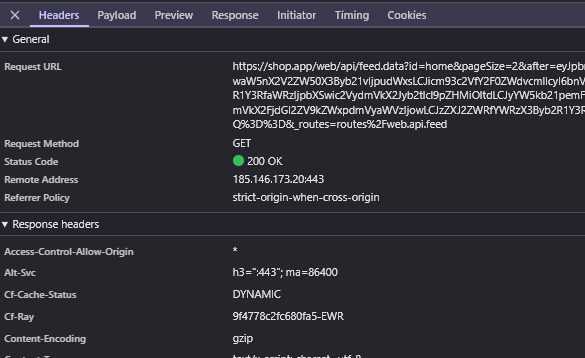
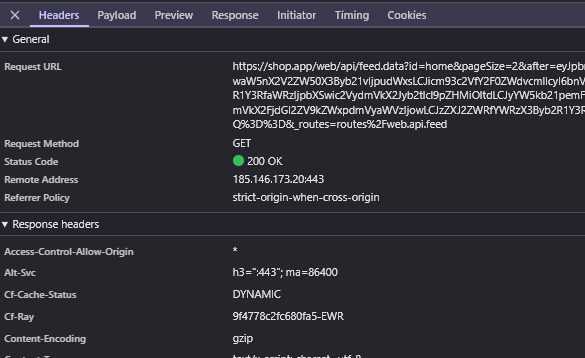
Even Shop.app, the consumer app where shoppers track packages and discover brands, pulls its feed from APIs behind Cloudflare.
Shopify has consolidated by design. One provider handles the storefronts that merchants sell through, the tools they use to run those stores, and the app where their customers come back to shop again.
Artificial Intelligence · San Francisco, CA · Claude, Claude API, Claude Code
Cloudflare
Cloudflare Access
Anthropic is the AI company behind Claude, a chatbot and assistant that competes head-to-head with ChatGPT. They also sell Claude through an API that other companies use to build AI features into their own products. The company is one of the major players in the current generation of AI labs.
Anthropic's Cloudflare footprint is broader than you might expect for a company this young. It protects both the customer-facing chat product and the internal tools their own employees use to log in.
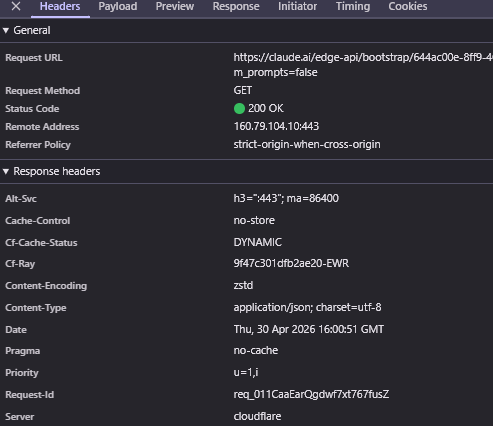
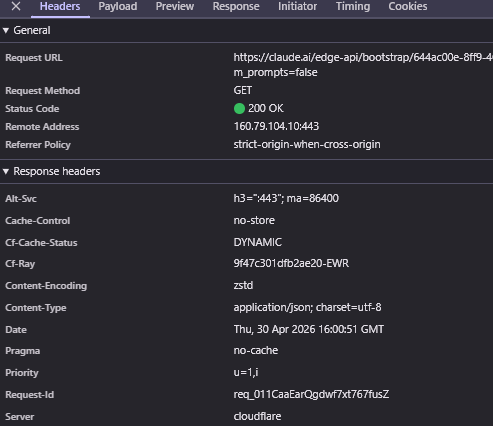
The consumer side is the obvious half. When someone uses Claude.ai to start a conversation, the chat interface fires off a backend request to kick things off, and the response comes back with a CF-Ray header confirming Cloudflare handled it.
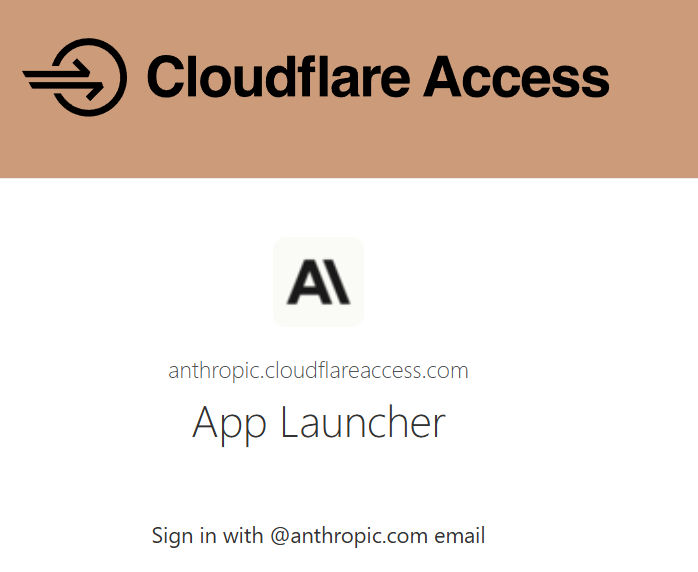
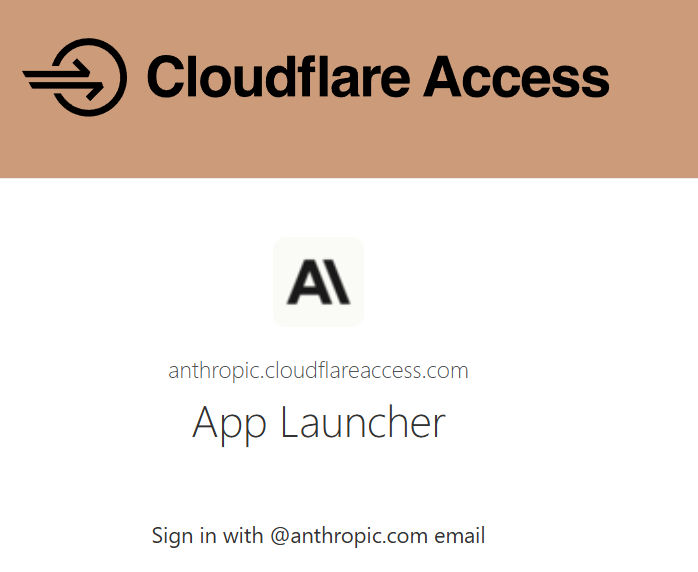
Less expected is how Anthropic uses Cloudflare on the inside. Some of their internal company tools sit behind Cloudflare Access, the product that handles employee sign-in to private apps. So when an Anthropic employee tries to reach an internal dashboard, Cloudflare is the gatekeeper checking who they are before letting them through.
There's a third layer too. Anthropic's marketing site, documentation, and developer console are built on a stack that includes Cloudflare alongside React, Next.js, and AWS Lambda. So whether someone is reading a blog post, hitting the API docs, or signing in to manage their billing, Cloudflare is part of the path.
Retail · Delft, Netherlands · Furniture and home goods
Cloudflare
Cloudflare Bot Management
Cloudflare Turnstile
IKEA is the Swedish furniture giant. They sell flat-pack furniture, kitchen cabinets, mattresses, and home goods through stores and a website that reaches dozens of countries. Their site is one of the most visited retail destinations in the world, with hundreds of millions of shoppers a year browsing products and placing orders.
IKEA isn't just a Cloudflare customer, they're a power user. The site stacks multiple Cloudflare products on top of each other, each handling a different layer of the security and traffic problem.
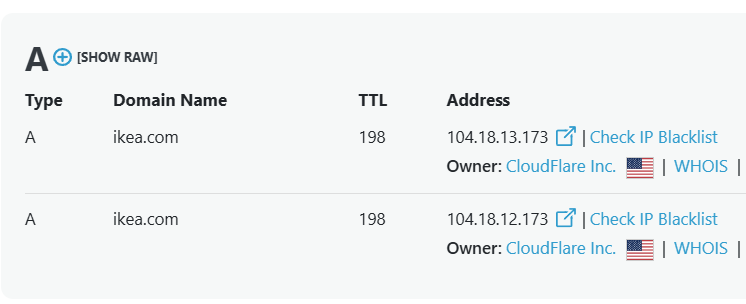
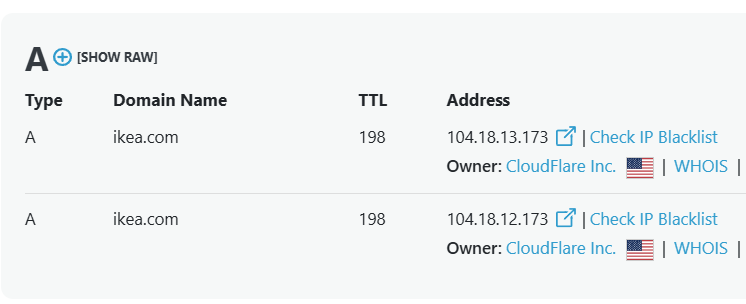
The foundation is straightforward. Ikea.com's DNS records point at Cloudflare, so every shopper who opens the site to browse a sofa or check stock at their local store hits Cloudflare first.
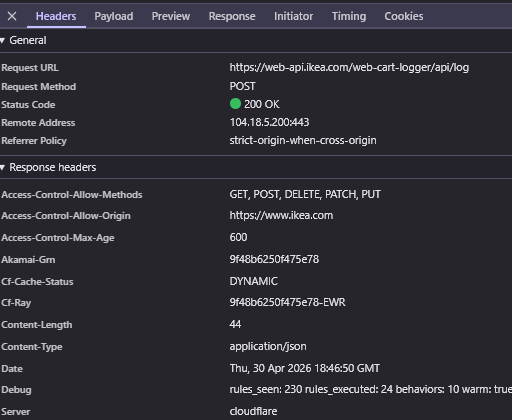
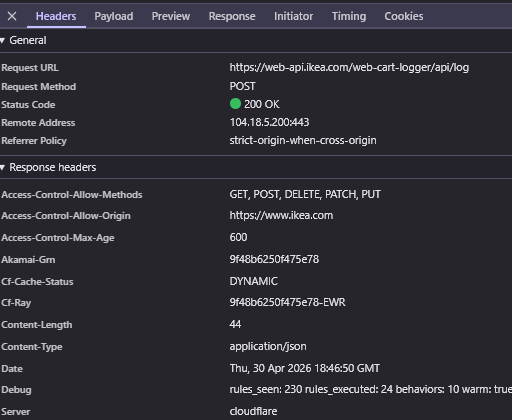
The background services that the site depends on, like the cart and logging APIs, also run through Cloudflare and return responses with a CF-Ray header.
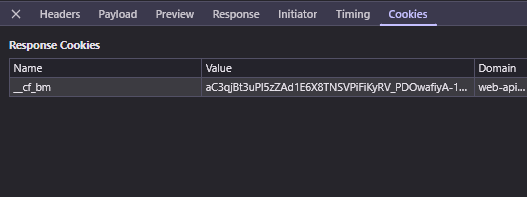
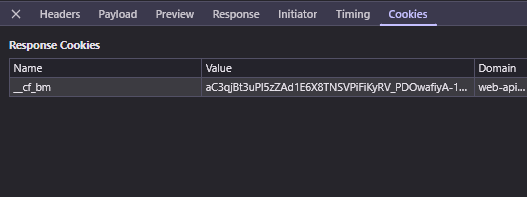
On top of that sits Cloudflare Bot Management. Every visit to ikea.com gets a __cf_bm cookie, a small token Cloudflare uses to track real shoppers across page loads and flag automated scrapers and scalpers trying to blend in. For a retailer constantly fighting checkout abuse and inventory scraping, that persistent fingerprint matters.
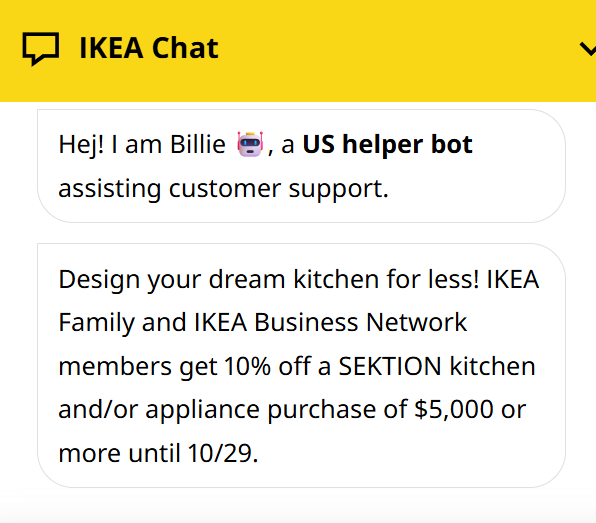
IKEA also runs Cloudflare Turnstile in the chat support widget. When a shopper opens chat on certain pages, Turnstile silently verifies the visitor is human in the background before connecting them to a support agent. The clearance token from that check then gets stored locally so the customer doesn't have to keep proving they're real on every click.
Retail · Boston, MA · Online furniture and home goods
Cloudflare
Cloudflare Access
Wayfair is one of the largest online furniture retailers in the world. They sell sofas, beds, rugs, and home goods to tens of millions of customers across the US and Europe. The site routinely absorbs huge spikes during sales like Way Day and Black Friday, when shoppers descend on the platform looking for discounts.
Cloudflare is Wayfair's front door for the entire customer experience, and one piece of that job is making sure the site stays standing when traffic surges.
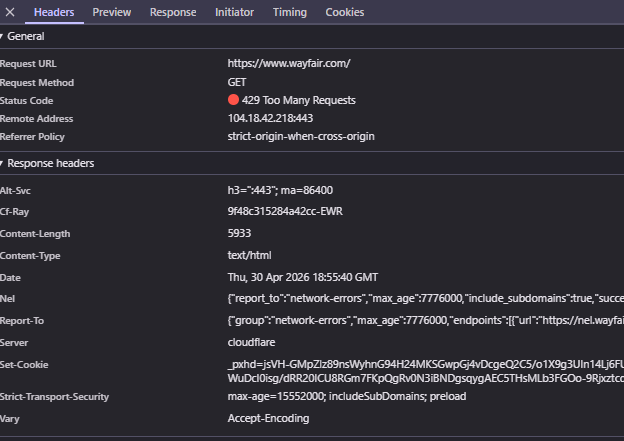
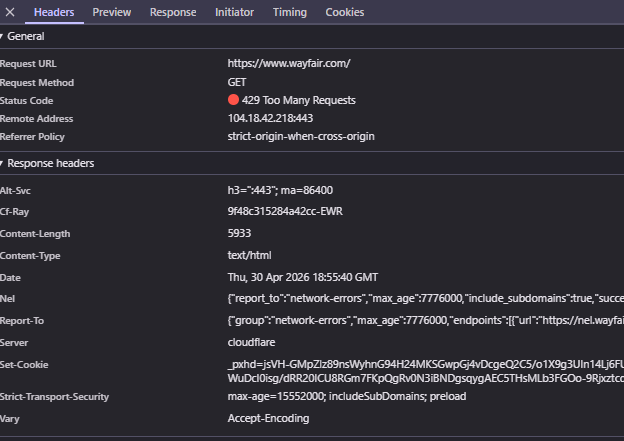
Wayfair.com's response headers show "Server: cloudflare" and a CF-Ray ID, the standard signature. But Cloudflare also handles rate limiting for them. Hit the site too fast and Cloudflare returns a 429 "Too Many Requests" error before that traffic ever touches Wayfair's own servers.
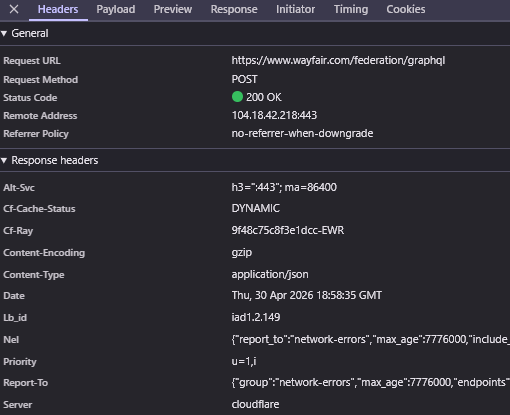
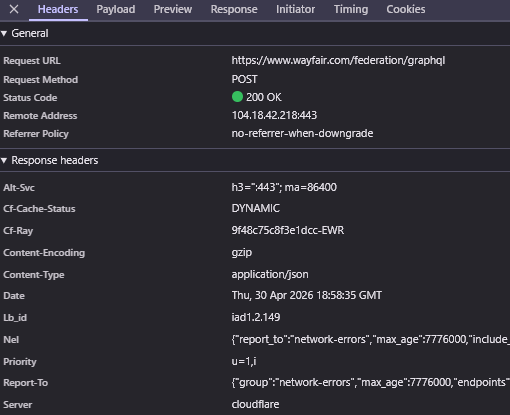
The same setup runs Wayfair's GraphQL API, the backend the website uses to fetch product listings, prices, and reviews. Whether a shopper is loading a category page or a single product page, the data behind it is being delivered through Cloudflare.
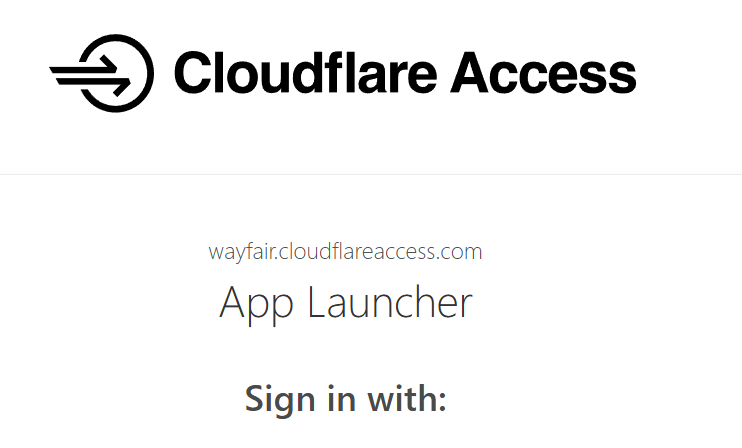
Wayfair also uses Cloudflare Access for internal tools. When an employee tries to reach an admin panel or internal dashboard, Cloudflare Access is what checks their identity and decides whether to let them through, which means the same provider handling customer traffic also handles employee logins.
Delivery · San Francisco, CA · On-demand delivery platform
Cloudflare
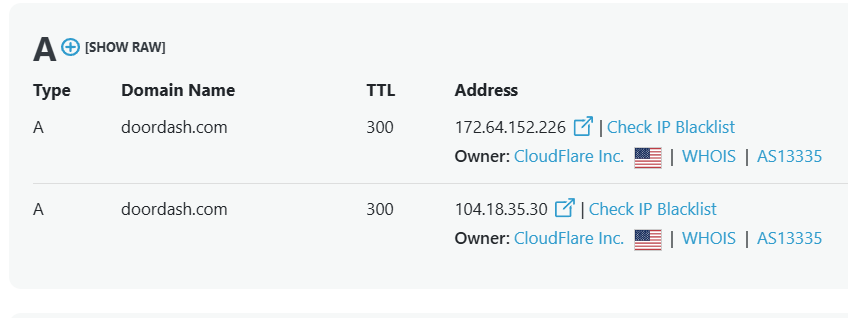
DoorDash is a delivery company. Most people know them for food delivery, but they've expanded into groceries, retail, and convenience items, operating across the US, Canada, and several other countries. After acquiring Deliveroo in 2025, the combined company powers delivery for tens of millions of customers and over a million merchants.
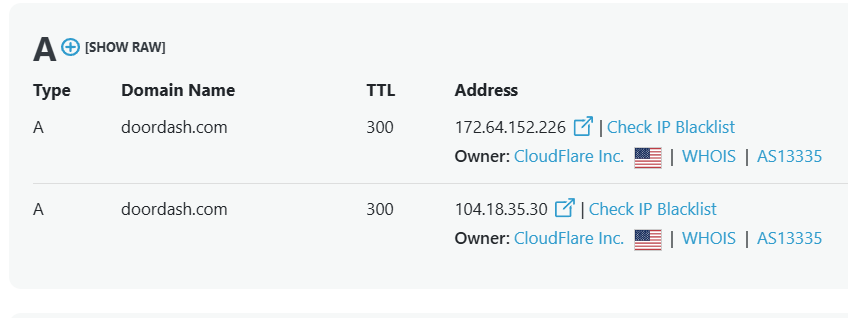
The basics look like every other large company on this list. DoorDash's domains sit behind Cloudflare, so when a customer opens the app or website to browse restaurants, Cloudflare answers first, serving cached content quickly, blocking malicious traffic with a web application firewall, and absorbing denial-of-service attacks before they ever reach DoorDash's servers.
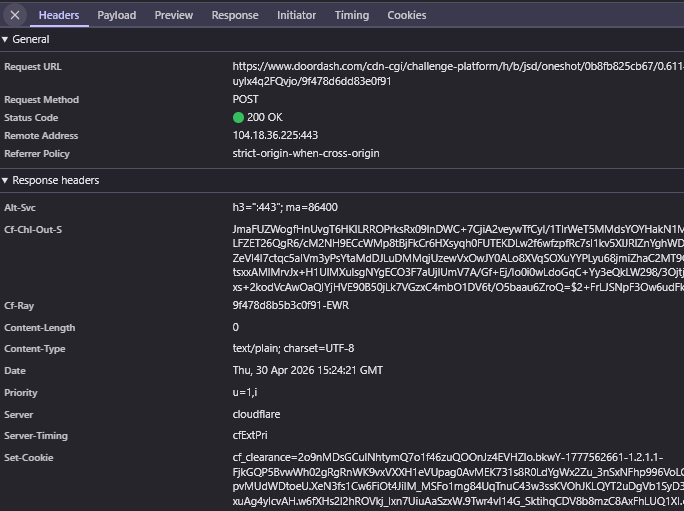
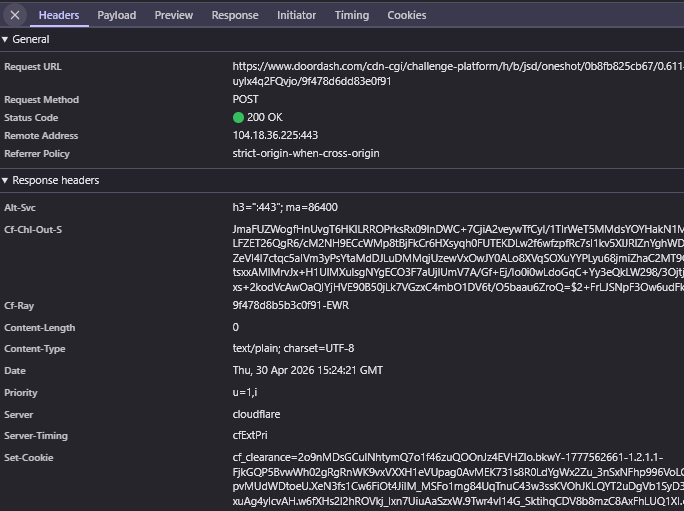
It also handles bot management. When the app makes a background request to load data, Cloudflare's challenge system filters out automated traffic pretending to be a real user.
What's more interesting is what DoorDash has built around Cloudflare. They have a dedicated engineering discipline called Edge, the entire layer where outside traffic meets their internal systems, with Cloudflare as one of the foundational pieces alongside other tools for proxies, load balancing, and DNS. After the Deliveroo acquisition, the same Edge team that runs DoorDash's traffic also runs the equivalent infrastructure for Deliveroo's food and grocery operations across the UK and Europe, and Cloudflare is part of what made consolidating those traffic paths possible.
Years ago DoorDash listed Cloudflare as one of many "nice to have" technologies for infrastructure engineers. Today there's a full team built around the discipline, with the work going from a piece of someone's job to a full-time specialty.
Software · Cambridge, MA · CRM, Marketing Hub, CMS Hub
Cloudflare
HubSpot is a software company that helps businesses run their marketing, sales, and customer service. They sell tools for things like sending email campaigns, managing leads, and building websites, and they have over 200,000 customers in more than 100 countries, ranging from small businesses to large enterprises.
HubSpot's Cloudflare relationship has a multiplier effect that few others on this list match. They don't just protect their own website. They protect every customer website built on their platform.
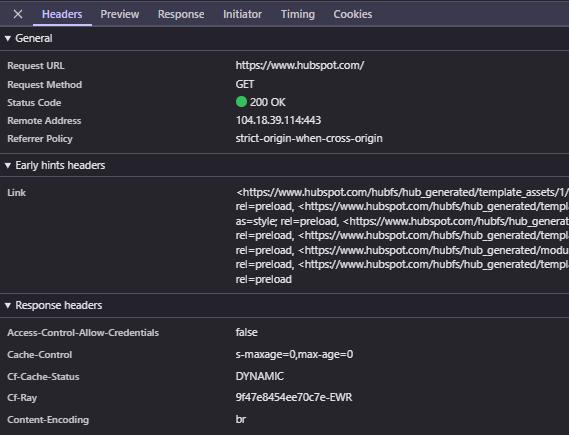
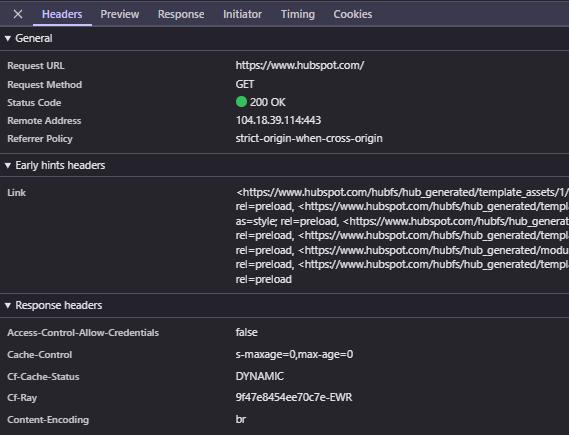
The basics are unremarkable. Visit hubspot.com and the request lands on Cloudflare first, with a CF-Ray header confirming it.
The leverage shows up in HubSpot's website builder, one of their flagship products. Hundreds of thousands of businesses use HubSpot to host their marketing sites, blogs, and landing pages, and those customer sites are served through HubSpot's infrastructure, which itself runs on Cloudflare. Visit a marketing page that's secretly running on HubSpot and the response headers tell the same story, with a CF-Ray header and Cloudflare listed as the server.
So a single relationship between HubSpot and Cloudflare ends up shielding hundreds of thousands of small business websites at once. The local plumber's site, the dentist's appointment page, and the coffee roaster's online shop all get the same protection, and none of those business owners had to know what Cloudflare was to benefit from it.
Financial Services · Foster City, CA · Payment network
Cloudflare
Cloudflare API Shield
Visa is one of the largest payment networks in the world. They sit between banks and merchants and process more than 250 billion transactions a year across more than 200 countries. When you tap your card at a coffee shop, swipe at a grocery store, or pay for something online, there's a good chance Visa's network is the one approving the transaction.
Visa runs one of the most security-sensitive infrastructure stacks in the world for the actual payments network, but for the consumer-facing properties, they hand the front door to Cloudflare.
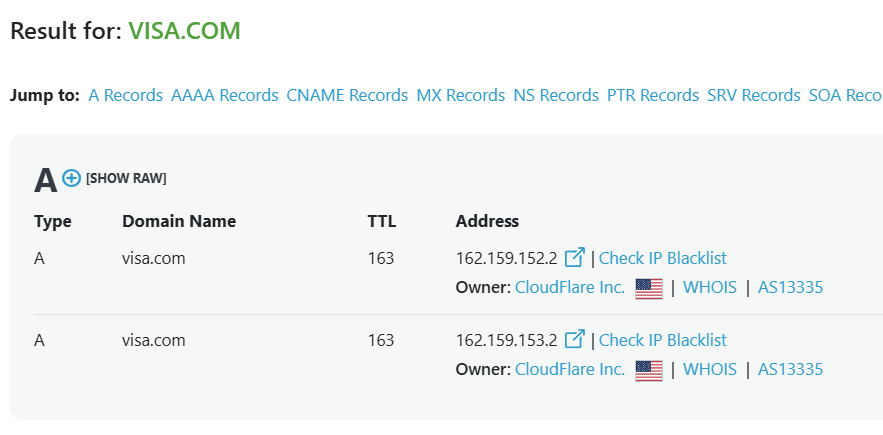
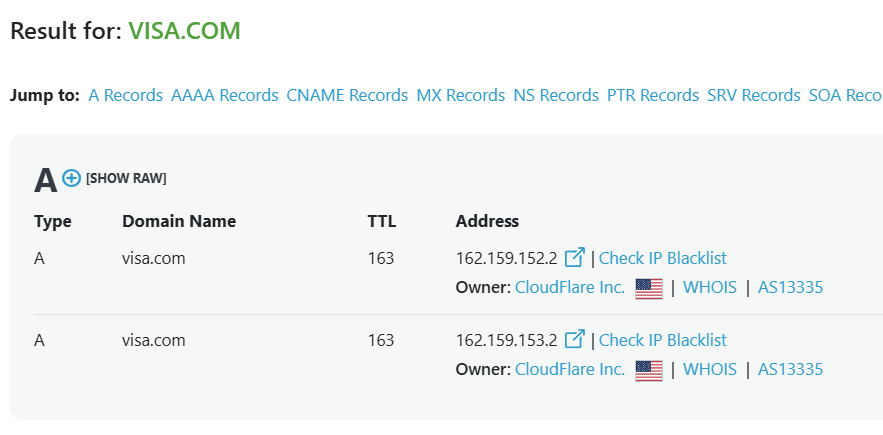
Visa.com's DNS points straight to Cloudflare. When a cardholder visits to check rewards, find a card, or read about a fraud alert, Cloudflare answers first.
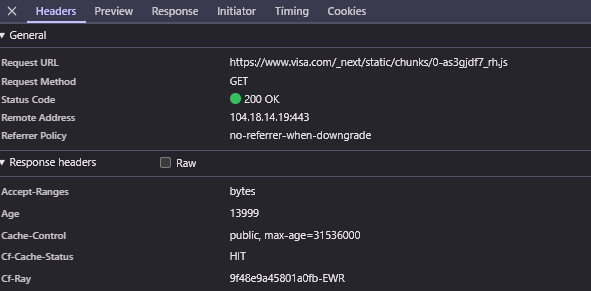
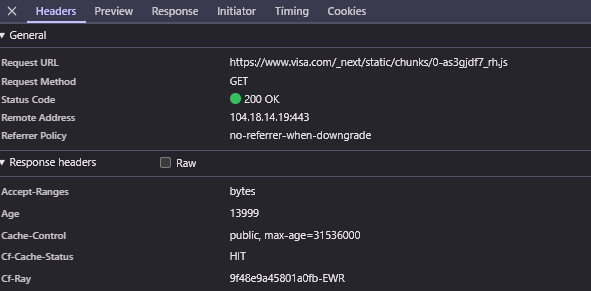
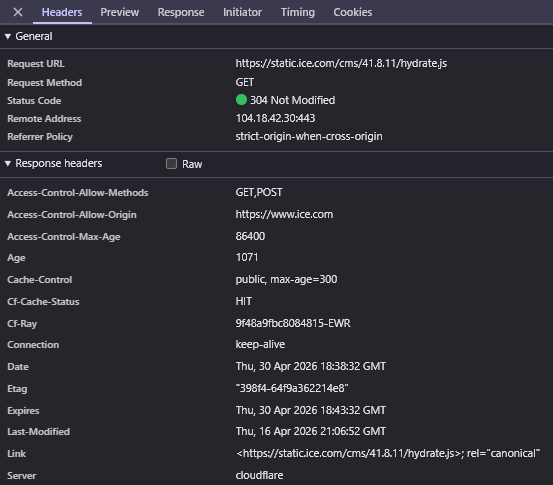
The static assets that make up the site, the JavaScript, images, and styling files, are also served through Cloudflare. Their response headers come back with a CF-Ray ID along with a "HIT" cache status, meaning Cloudflare served the file from its own network instead of pulling it from Visa's servers.
Behind the scenes, Visa has built a team responsible for managing CDN providers, including Cloudflare and Akamai. Their Web Application Firewall team specifically lists Cloudflare API Shield as one of the API security solutions they work with. So beyond just serving the website, Cloudflare is part of how Visa protects API-level traffic from common attacks like SQL injection, cross-site scripting, and bot abuse.
Financial Services · Atlanta, GA · NYSE, ICE Mortgage Technology, ICE Data Services
Cloudflare
Intercontinental Exchange, better known as ICE, runs financial markets. They own the New York Stock Exchange and a long list of other trading platforms, exchanges, and data services. They also have a large mortgage technology business that sells software to banks and lenders. The company processes trillions of dollars in trades and is one of the most important pieces of plumbing in the global financial system.
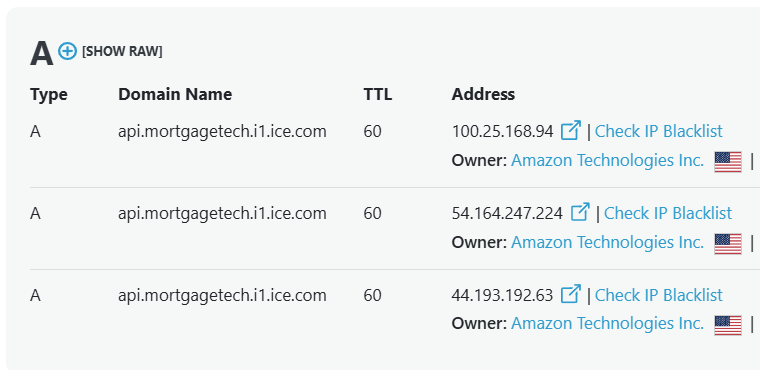
ICE has split their infrastructure deliberately. Cloudflare handles the public-facing website and the static content that goes with it, while their backend APIs run on Amazon Web Services. Two providers, two clearly defined jobs.
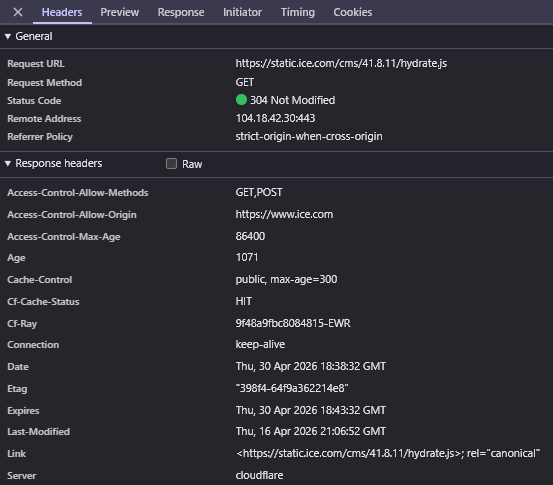
Visit ice.com and the page is delivered through Cloudflare's network. The static files that make up the site, like JavaScript and CSS, also come from Cloudflare with a CF-Ray header on the response.
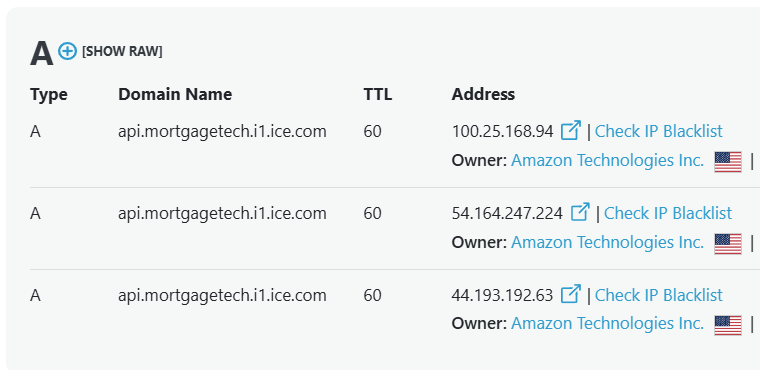
The split shows up clearly in their mortgage technology APIs. The backend that powers their lending products lives at api.mortgagetech.i1.ice.com, and its DNS records point straight to Amazon's servers. So when a bank makes a real backend call to fetch data or process a loan, that request goes to AWS, not Cloudflare.
Each provider gets the work it does best. Cloudflare's network is built for serving the same content to lots of people quickly from locations all over the world, which makes it a natural fit for a public website. AWS is built for running backend logic and storing the actual data that powers the business. ICE has drawn a line between the two and lets each handle its piece.
Financial Services · Brussels, Belgium · 5,000+ employees
WAF
SSL/TLS
mTLS
Euroclear is a giant behind-the-scenes player in global finance. They handle the settlement of stock and bond trades, basically making sure that when banks buy and sell securities, the money and shares actually change hands correctly. Over 2,000 financial institutions around the world rely on them.
What stands out about how Euroclear uses Cloudflare is that they don't trust any single security tool to stand alone. They run a "dual layer" web application firewall strategy, where Cloudflare sits as one layer of protection and Imperva sits as another. Two different vendors, stacked on top of each other, both inspecting traffic before it ever reaches the applications behind them.
The logic is simple. If one firewall misses an attack or has a bad day, the other one is still there. For a company that processes the financial transactions of major banks, "good enough" security isn't good enough. They want belt and suspenders.
Cloudflare's role in that stack is the front door. It handles the encrypted traffic coming in from clients around the world, including HTTPS, TLS, and the stricter mutual TLS where both sides have to prove who they are with certificates. It also plugs into the login systems that decide who's allowed through.
Behind all of this is a small team that runs the security platform around the clock. They take rotating shifts so someone is always watching, since attacks don't keep business hours. They also write a lot of code with tools like Terraform and Ansible, so that pushing a new firewall rule to Cloudflare is something they can automate rather than do by hand.

 SymbyAI
SymbyAI
 KNACX Corporation Limited
KNACX Corporation Limited
 The Complete Leader
The Complete Leader
 Planning and Development Agency
Planning and Development Agency
 PolySciTech Division: Akina, Inc.
PolySciTech Division: Akina, Inc.
 Borg Design Inc.
Borg Design Inc.
 Twintec Group
Twintec Group
 Inter-Strap Packaging Systems, Inc.
Inter-Strap Packaging Systems, Inc.
 Salutem Management
Salutem Management
 Catholic Education Foundation - Kansas City, KS
Catholic Education Foundation - Kansas City, KS
 Expert du Sommeil
Expert du Sommeil
 Cricut
Cricut
 A-1 Sewer & Septic Service & A-1 HVAC
A-1 Sewer & Septic Service & A-1 HVAC
 TONAL LATAM
TONAL LATAM
 Modine HVAC
Modine HVAC
 The Sanitaryware Company
The Sanitaryware Company
 Union League Boys & Girls Clubs
Union League Boys & Girls Clubs
 Budder
Budder
 Tarrytown Expocare Pharmacy
Tarrytown Expocare Pharmacy
 Direktoratet for eksportkontroll og sanksjoner
Direktoratet for eksportkontroll og sanksjoner
 OpenAI (ChatGPT)
OpenAI (ChatGPT)
 Microsoft
Microsoft
 X
X
 AbbVie
AbbVie
 Shopify
Shopify
 Anthropic (Claude)
Anthropic (Claude)
 IKEA
IKEA
 Wayfair
Wayfair
 DoorDash
DoorDash
 HubSpot
HubSpot
 Visa
Visa
 Intercontinental Exchange
Intercontinental Exchange
 Euroclear
Euroclear